The container landscape on macOS has long been dominated by solutions like Docker and Podman, which rely on a traditional Linux VM layer to run containers. However, Apple’s open-source Containerization framework and accompanying Container CLI announced at WWDC2025 are challenging this status quo.
This new architecture, optimised for Apple Silicon, introduces a fundamentally different approach that prioritizes native integration and hardware-level isolation. Let’s break down what Apple Container is and explore the core architectural differences that set it apart from daemonless rivals like Podman.
What Is Apple Container ?
Apple Container is an official, open-source container runtime and framework created by Apple, built in Swift.
It’s primary goal is to provide developers with a native, high-performance container experience on macOS (specifically leveraging the Virtualization framework on Apple Silicon hardware). It is designed to work with existing OCI-compliant container images, meaning you can pull and run standard images from registries such as Docker Hub or Red Hat registry using Apple’s new tools.
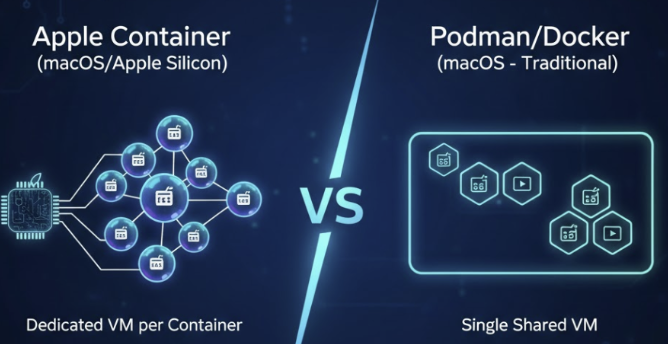
While tools like Podman on macOS run containers inside a single, shared Linux virtual machine (a necessary layer on macOS/Windows), Apple Containerization introduces a radical alternative: a dedicated, lightweight virtual machine for every single container.
Apple Container vs. Podman: The Architectural Divide
Podman (which stands for Pod Manager) is a popular, open-source, daemonless container engine that manages pods and containers based on the OCI specifications. On a native Linux host, Podman uses the host’s kernel namespaces and cgroups for isolation. When running on macOS, Podman typically utilizes a tool like podman machine to create a single, large Linux VM, and then all containers share the kernel within that single VM.
Apple Container entirely bypasses the shared-VM model, making the isolation mechanism the key difference. This leads to profound architectural consequences.
Here are the top 5 architectural differences between Apple Container’s design and the shared-kernel/shared-VM model used by Podman and other traditional engines:
1. Isolation Boundary: Hypervisor vs. Namespaces
| Feature | Apple Container | Podman (Traditional) |
| Isolation Mechanism | Dedicated VM/Hypervisor-based isolation. Each container is fully isolated at the hardware level by the macOS Virtualization framework. | OS Kernel Namespaces and Cgroups. Containers share a single Linux kernel, relying on OS features to partition resources and visibility. |
| Security Implication | Provides superior hardware-level security isolation because a compromise in one container cannot spread to the shared host kernel or other VMs. | A compromise in the shared kernel could potentially affect all running containers, though this is mitigated by robust kernel features. |
2. Kernel Usage and Footprint
Apple Container uses an optimized Linux kernel configuration specifically designed for minimal footprint and sub-second startup times. This kernel is ephemeral—it exists only for the life of its single container. Podman, by contrast, relies on either the native host kernel (Linux) or a single, persistent Linux VM kernel (macOS).
3. The Custom Init System: vminitd
Inside every lightweight Apple Container VM runs vminitd, a custom init system written entirely in Swift. This minimalist process is designed to handle core virtualization tasks like:
- IP address assignment.
- Filesystem mounting of container block devices.
- API management for host-container communication.
This custom, constrained init system operates without standard core utilities or traditional libc implementations, greatly reducing the potential attack surface. Traditional containers rely on standard Linux process management or simpler init wrappers like Tini.
4. Implementation Language and Platform Optimisation
The Apple Containerization framework is a Swift-native implementation. It leverages the Swift Static Linux SDK and musl for static linking. This means the binaries are self-contained and heavily optimized for the Apple Silicon (ARM) architecture.
Podman is primarily written in Go and designed for cross-platform compatibility based on standard Linux and OCI conventions. Apple’s Swift-native approach allows for a deeper, more cohesive integration with the macOS operating system and development ecosystem.
5. Networking and Resource Model
The VM-per-container approach fundamentally simplifies networking for containers. Each container’s dedicated VM can be configured to manage its own networking stack, allowing containers to bind to standard ports without conflicts.
While a single shared-VM model (like the one used by Podman on macOS) can lead to inefficient resource allocation for the large background VM, the Apple model manages resources for many lightweight, ephemeral VMs. This shift provides more precise, granular, hardware-level isolation, although the hypervisor overhead is present for every container.
Conclusion
Apple Container represents a significant architectural evolution for running containers on macOS. By embracing the VM-per-container model, Apple prioritizes superior security isolation and native, optimized performance on its own platform.
While Podman and the mature Docker ecosystem still offer crucial advantages in cross-platform compatibility and extensive tooling (like Docker Compose equivalents), Apple’s technical foundation is solid. For developers prioritising performance and deep, secure integration on Apple Silicon, Apple Container is poised to become the compelling native standard.